On a Monday afternoon in May 2019, someone robbed the Call Federal Credit Union in Midlothian, Virginia, a small town just outside of Richmond. Police knew that an unidentified man entered the bank at around 4:50 PM and handed the teller a note demanding “at least 100K.” They knew that he pulled out a silver and black gun and directed the bank manager to open the vault. And they knew that he left on foot with $195,000 in cash. But by mid-June, the detective working the case, Joshua Hylton, had run out of leads.
Surveillance footage showed, however, that the suspect walked into the bank while using a cell phone. So, Hylton went to a judge and got a “geofence” warrant—a special type of warrant that allows the government to draw a virtual “fence” around a geographic location and demand that tech companies hand over information about their users within the fenced-in area at a given time.
In effect, geofence warrants work like a digital dragnet, empowering cops to rummage through your phone data if they think a crime may have occurred a few blocks away from you. And on Monday, April 27, the Supreme Court will hear oral argument and debate whether the Constitution has any problem with that.
In this case, Chatrie v. United States, Hylton served Google with a geofence warrant that spelled out a three-step process. First, it requested anonymized location data for everyone with a Google account who was within a 150-meter radius of the bank’s approximate latitude and longitude coordinates between 4:20 PM and 5:20 PM on the day of the robbery. Second, the warrant requested additional anonymized location information—including travel outside the fence from 3:50 PM to 5:50 PM—for a subset of the initial list of Google users to be determined by the police. And third, the warrant requested user identity information—such as someone’s name, birthday, phone number, and email address—for another to-be-determined subset of the earlier list.
Step One of the warrant swept up 19 people who were in or near the bank and a neighboring church the afternoon of the robbery. Hylton then asked Google for Step Two and Step Three data on all 19 users. Google refused, concerned that Hylton deviated from the sequential steps and didn’t attempt to narrow down the list, as required by the search warrant. So Hylton modified his request and asked for Step Two data—with the extra hour of information about people’s whereabouts beyond the geofence—for nine of the users. Why those nine? Hylton didn’t say. But Google complied.
Finally, at Step Three, Hylton asked Google to “unmask” three of the nine anonymized users, again without explaining his reasoning or consulting a judge. Again, Google complied. One of the three users identified was Okello Chatrie. Law enforcement then got a warrant to search his residence. And there, in August 2019, cops found two demand notes, a silver and black gun, and nearly $100,000 in cash, including bills wrapped in bands signed by the bank teller. A month later, a grand jury indicted Chatrie on two charges related to armed robbery.
Chatrie tried to suppress the uncovered evidence as the fruits of an unconstitutional search of his phone data. The Fourth Amendment prohibits “unreasonable searches and seizures.” And to that end, it explicitly requires that warrants be based “upon probable cause,” and that they “particularly” describe “the place to be searched, and the persons or things to be seized.”
This means that police aren’t supposed to go on fishing expeditions willy-nilly. Instead, before they conduct a search, they’re supposed to go to a judge and show that they have “probable cause” to search a specific person or place. But here, Hylton indiscriminately searched the phones of people inside a circle with a diameter spanning three football fields, and developed his suspicion along the way.
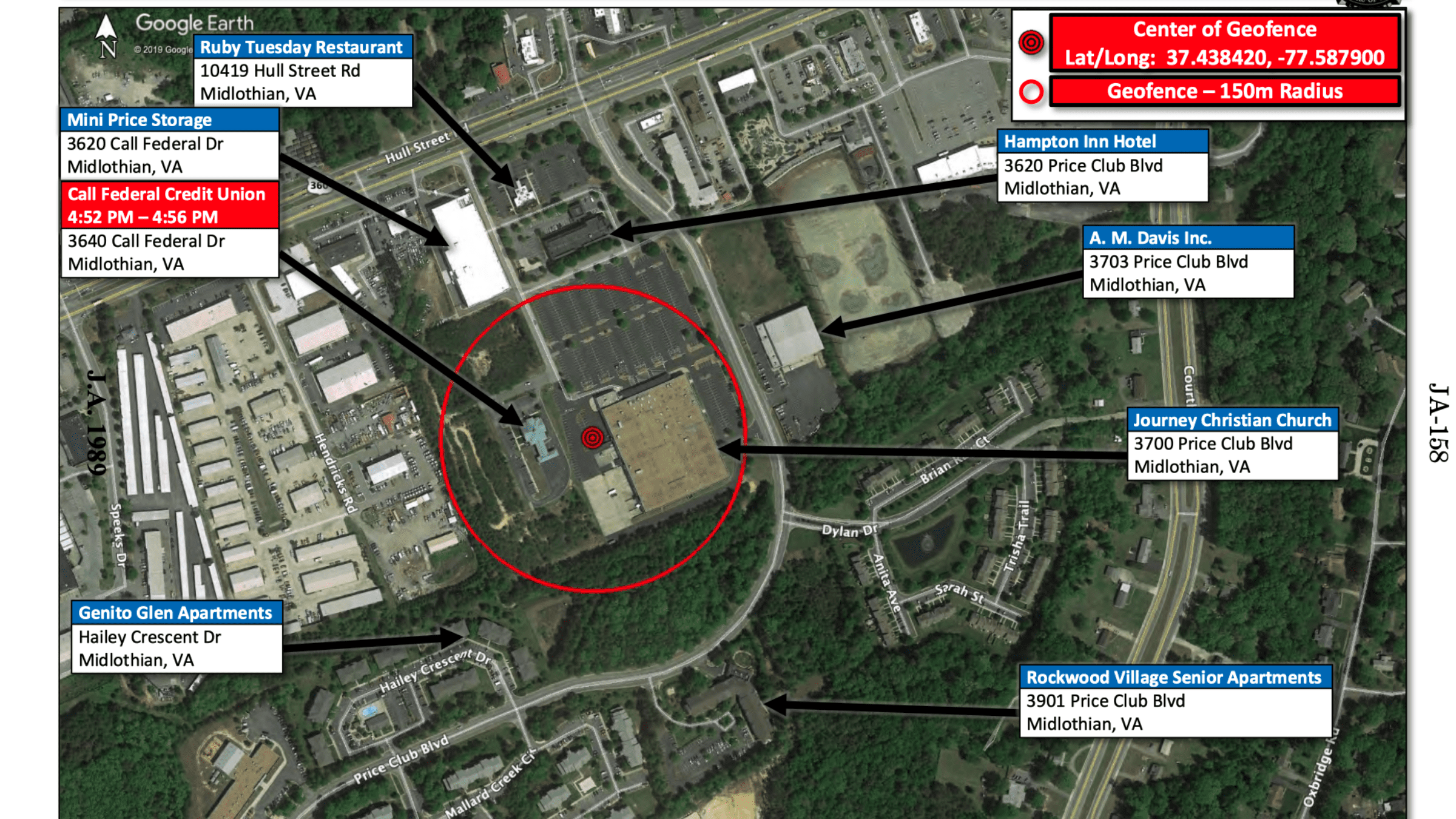
The area of the geofence warrant (via Chatrie cert petition)
Federal district judge M. Hannah Lauck agreed with Chatrie that the geofence warrant was “invalid” because, she wrote, it “lacked any semblance” of the particularized probable cause that the Fourth Amendment requires. Nevertheless, she declined to suppress the evidence at his trial, concluding that it was reasonable for Hylton to rely on the warrant “in the face of novel technology” and without any action from Congress. Chatrie entered a conditional guilty plea, reserving his right to appeal.
Chatrie’s appeal to the Fourth Circuit didn’t fare much better. In July 2024, a divided three-judge panel held that Hylton didn’t conduct a search that violated the Fourth Amendment. In fact, Judge Julius Richardson wrote for the majority, Hylton didn’t conduct a search at all, since Chatrie had “voluntarily exposed this information to Google.”
To justify this conclusion, the majority pointed to those terms and conditions that pop up and everyone scrolls past without reading whenever they install new apps on their phones. When Google prompts users to enable location history, text appears informing the user that doing so “saves where you go with your devices.” The permission screen also says “this data may be saved and used in any Google service where you were signed in to give you more personalized experiences.” The Fourth Circuit concluded that Chatrie “cannot now claim to have had a reasonable expectation of privacy” in his location information because he already shared that information with Google. Apparently, if you let Google Maps save your frequent destinations so you can easily pull up directions, you assume the risk of Google exposing all of your movements to the cops.
Chatrie petitioned for the full Fourth Circuit to rehear the case, and the court affirmed in a one-sentence decision that, simultaneously, produced nine separate opinions with wildly different analyses. Seven judges concluded that there was a search and it violated the Constitution. (Six of those seven judges, however, agreed with the district court that the search fell into the “good faith” exception for cops, and the evidence shouldn’t be suppressed.) Seven other judges endorsed the panel’s view that agreeing to give information to Google is the same as agreeing to give information to the police. One final judge declined to decide one way or the other whether there was a Fourth Amendment search, opting to “wait” before making any “sweeping constitutional pronouncements” because of what he called “a shallow well of information and legal authority” and “a litany of unanswered questions.” With a stalemate, Chatrie lost the appeal.
Chatrie has now appealed to the Supreme Court. And in an amicus brief, a group of law and technology professors forcefully challenge the idea that tapping ‘yes’ on location sharing so a Lyft driver knows where to pick you up is tantamount to knowingly consenting to government surveillance. For one thing, they point out, “companies give users little choice in whether and how this data is collected,” so the presumed consent is “hardly voluntary” to begin with.
Furthermore, they argue, Google’s primary permission screen doesn’t “inform users that it would automatically collect their location data every two minutes at a level so precise it includes which floor of a building they were on.” Nor does it tell users that Google would continue collecting location data even “when they deleted the app to which they gave permission.” And, most relevant here, it doesn’t tell users “that their location data might be turned over to the police in the absence of probable cause that they committed a crime.” Indeed, as the Innocence Project shares in a separate amicus brief, there are already documented instances of geofence warrants leading to wrongful arrests of people who just happened to be in the wrong place at the wrong time.
The question now before the Supreme Court is whether the execution of this specific geofence warrant violated the Fourth Amendment, but the answer will affect many more people than just Chatrie. Google received its first geofence warrant in 2016. Today, Google receives over 11,000 geofence requests a year, representing over a quarter of all warrants it receives in the United States. And hundreds of millions of Google users have location history enabled on their devices. Chatrie v. United States will determine if, when people switch these features on, they unknowingly relinquish their constitutional rights.